Elastic Stack vulnerability can lead to data theft and denial-of
4.7 (531) · $ 15.00 · In stock
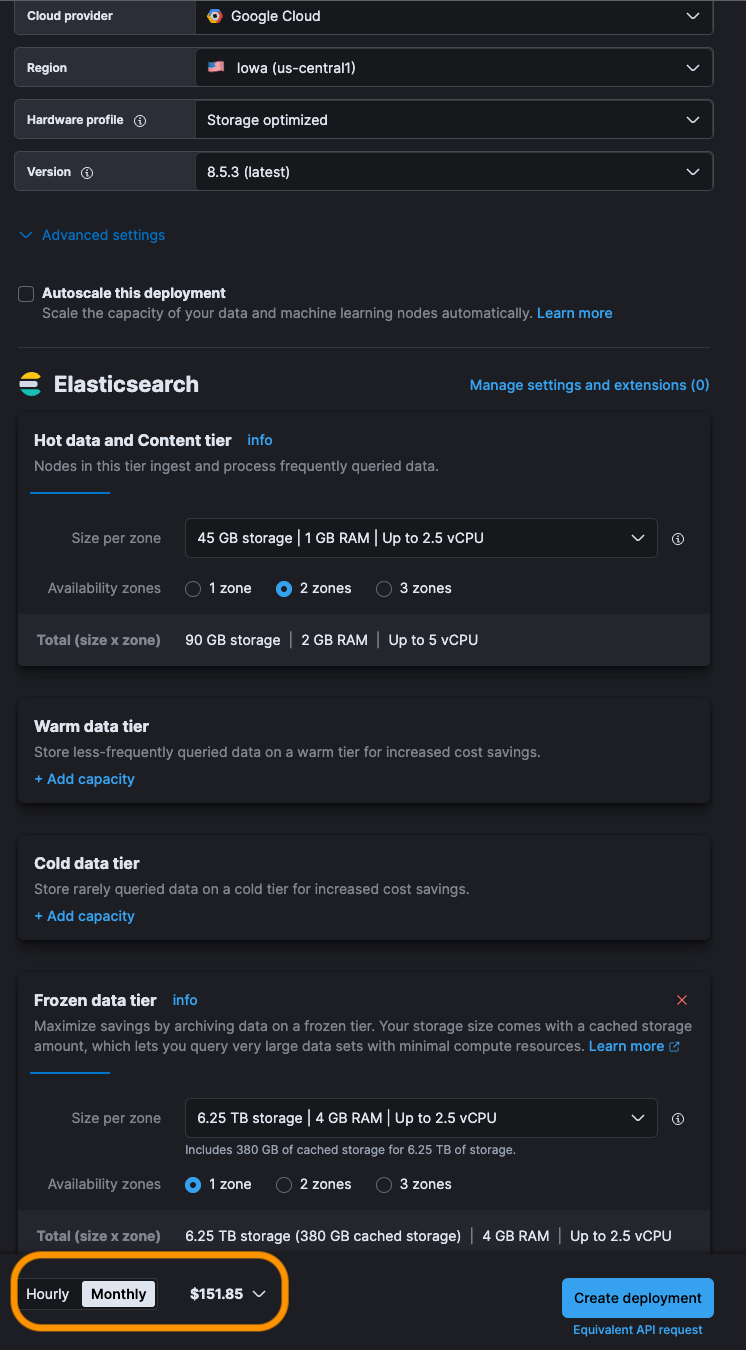
Researchers from Salt Security Inc. today detailed a new application programming interface vulnerability that can lead to attacks on Elastic Stack.The vulnerability stems from a faulty implementa

Project Ava: On the Matter of Using Machine Learning for Web Application Security Testing – Part 4: Architecture and Design, NCC Group Research Blog

Data Breaches: Complete Guide to Threats, Tools and Tactics
Elastic on Elastic: How InfoSec uses the Elastic Stack for vulnerability management
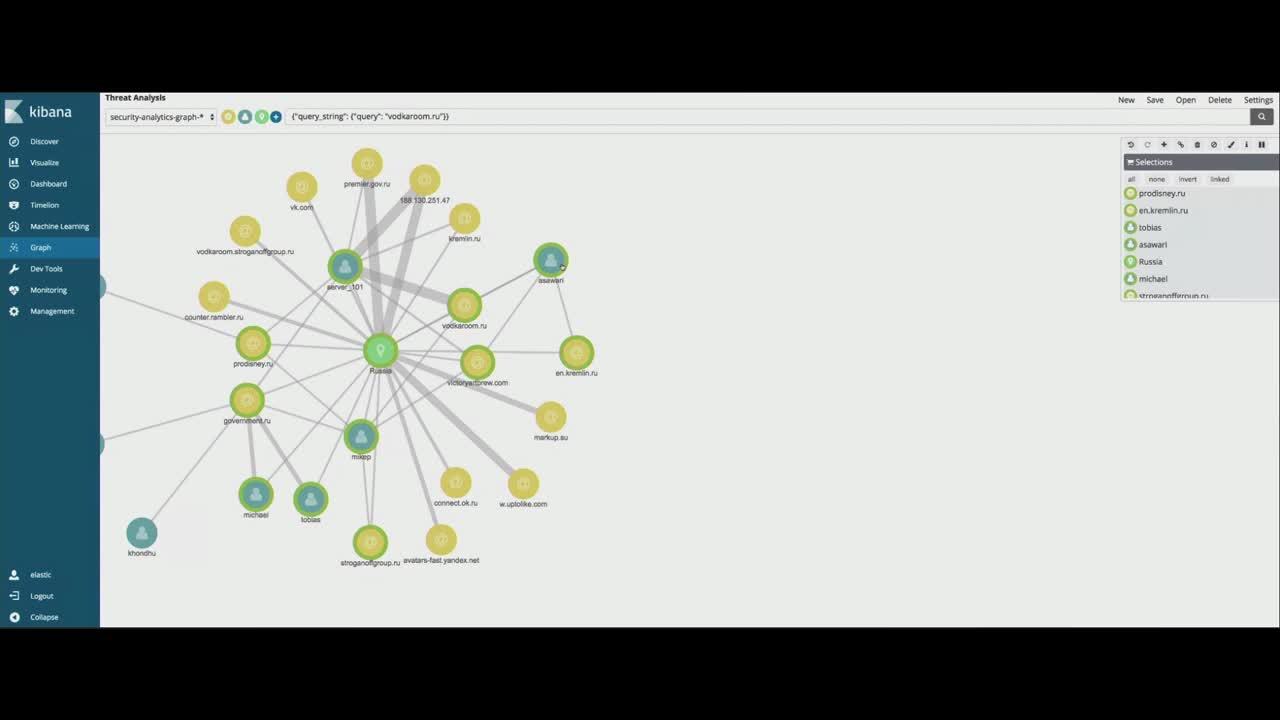
Elasticsearch Security Analytics: Vulnerability Scans

Log in to Elastic Stack with WSO2 Identity Server with OAuth2/OIDC, by Shan Chathusanda Jayathilaka

Architect defense-in-depth security for generative AI applications using the OWASP Top 10 for LLMs
5 Common Elasticsearch Mistakes That Lead to Data Breaches - Coralogix

API Threat Research Elastic Stack Misconfiguration Allows Data Extraction
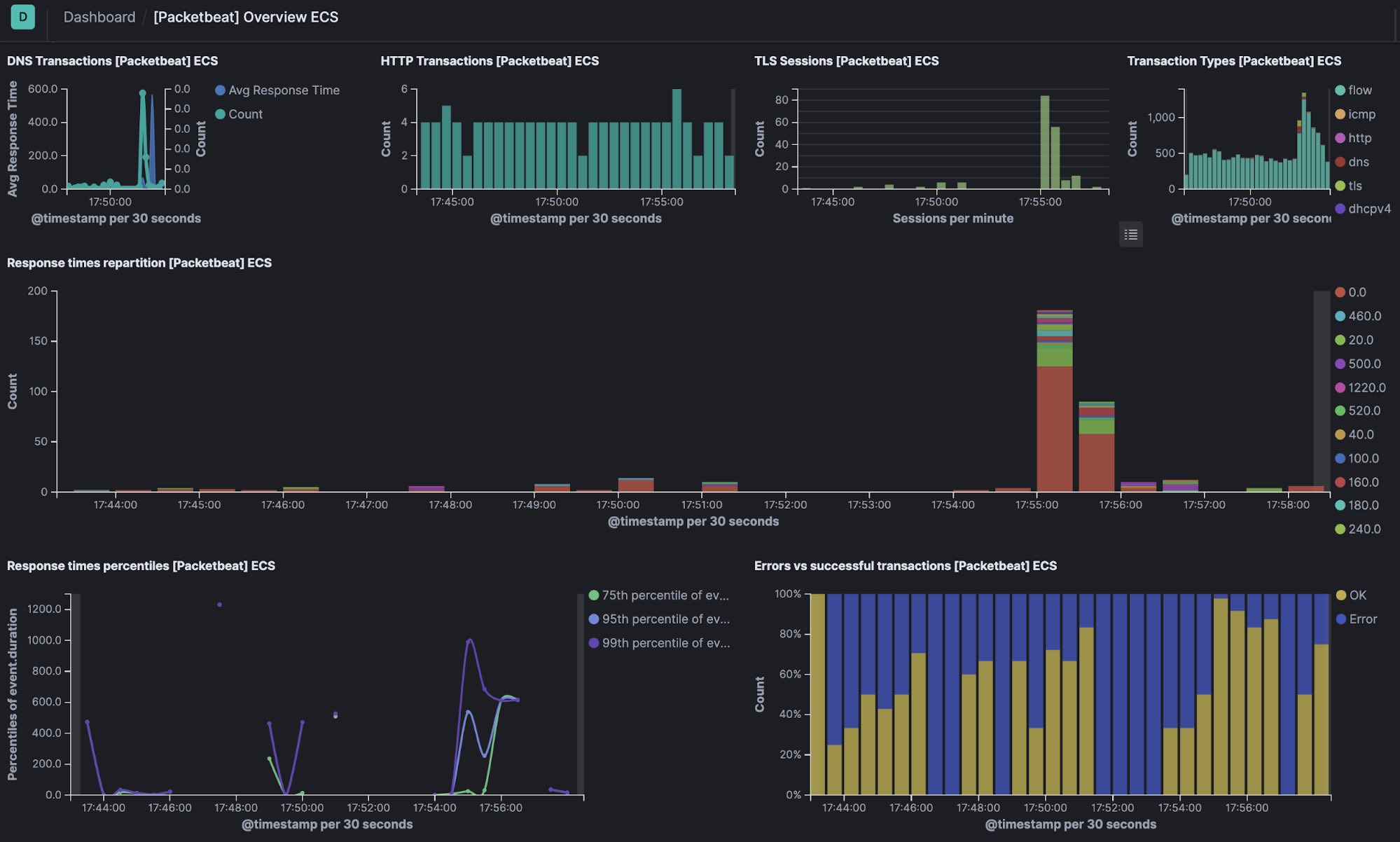
Unlocking security data sources with the Elastic Stack

Denial-of-service attack - Wikipedia

denial of service Security Magazine

Top 5 most dangerous injection attacks












